By Rob Borkowski
WASHINGTON, D.C.—President Barack Obama has expelled 35 Russian intelligence agents, shut down two Russian compounds in Maryland and New York, and released information about that country’s civilian and military cyber activity, measures Congressman Jim Langevin praised while imploring President Elect Donald Trump to end his denial that Russian hackers interfered with the 2016 Presidential election.
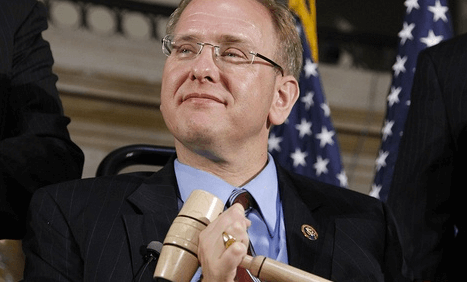
“Interference in our electoral processes cannot be tolerated, and I am encouraged that President Obama is taking steps to respond to Russian attempts to undermine faith in and influence the 2016 federal elections. In particular, I commend the President for using a full range of response options, including economic, diplomatic, and cybersecurity actions. As nations increasingly use hacking and other cyber operations to advance their objectives, it is imperative that the United States respond firmly to attacks targeting our interests,” Langevin said.
In a statement posted to whitehouse.gov, Obama announced he also sanctioned nine entities and individuals: the GRU and the FSB, two Russian intelligence services; four individual officers of the GRU; and three companies that provided material support to the GRU’s cyber operations.
Those companies, according to a press briefing transcript also posted today, are the Special Technology Center St. Petersburg, Zorsecurity, and the Autonomous Noncommercial Organization, (ANO PO KSI) — which have provided cyber services and training to the GRU.
The Secretary of the Treasury is also designating two Russian individuals for using cyber-enabled means to cause misappropriation of funds and personal identifying information. The briefing transcript identifies those individuals as Evgeniy Bogachev and Aleksey Belan, described as notorious cyber criminals responsible for havoc in the international financial system, including against American companies.
The State Department is also shutting down two Russian compounds, in Maryland and New York, used by Russian personnel for intelligence-related purposes, and is declaring 35 Russian intelligence operatives as “persona non grata”.
The Department of Homeland Security and the Federal Bureau of Investigation are also releasing declassified technical information on Russian civilian and military intelligence service cyber activity, to help network defenders in the United States and abroad identify, detect, and disrupt Russia’s global campaign of malicious cyber activities.
“The President’s actions are also notable because they have a deterrent effect beyond the punishment of Russians directly involved with or supporting the information warfare operation. By releasing formerly classified threat indicators, the Department of Homeland Security and FBI have exposed Russian hacking infrastructure and made it much easier for individuals and businesses around the world to protect themselves from Russian aggression. I strongly encourage network administrators to read the Joint Analysis Report hosted by the U.S. Computer Emergency Readiness Team and take action to protect their systems,” Langevin said.
Obama effected the actions by amending the Cyber Executive Order, originally issued originally in April 2015.
President Elect Donald Trump, who has denied Russian interference in the election, has said the country should move on, but told the New York Times he would discuss the issue with intelligence officials.
Langevin said the actions were important to show Russian officials that interference in American institutions and elections will not be brushed off without a response.
“However, we must continue to investigate ways to improve our resiliency and protect ourselves from future such operations, which is why I again call on Speaker Ryan to empower a Select Committee on Cybersecurity to look into the attacks. I also hope that the President-elect will use this moment to stop his utterly unfounded innuendo that that there is any uncertainty regarding Russian involvement in the hacks,” Langevin said.